IoT adoption continues to grow across industries. Businesses now deploy connected devices in manufacturing, healthcare, logistics, and smart cities. Recent reports show that the number of IoT devices will exceed 30 billion by 2030. At the same time, security risks are rising rapidly. Around 60% of organizations report IoT-related security incidents. Many attacks target weak device configurations and unprotected firmware.
Security gaps often begin early in development. Traditional approaches add security at later stages, which increases risk and cost. This is where a DevSecOps approach becomes important.
What is DevSecOps in IoT Development?
DevSecOps combines development, security, and operations into one continuous process. It ensures that security is not a separate step but part of the entire lifecycle.
DevSecOps = Development + Security + Operations
In IoT systems, DevSecOps covers:
- Device firmware
- Communication protocols
- Cloud platforms
- APIs and applications
This approach helps detect issues early and reduce vulnerabilities.
Why IoT Security Needs DevSecOps
IoT environments are complex and distributed. Devices connect to networks, cloud systems, and external services. Each connection point can create a risk.
Key reasons to adopt DevSecOps:
- Devices operate in remote and uncontrolled environments.
- Firmware updates can introduce vulnerabilities.
- Data moves across multiple systems.
- Attack surfaces increase with more connected devices.
Without early security integration, risks grow quickly.
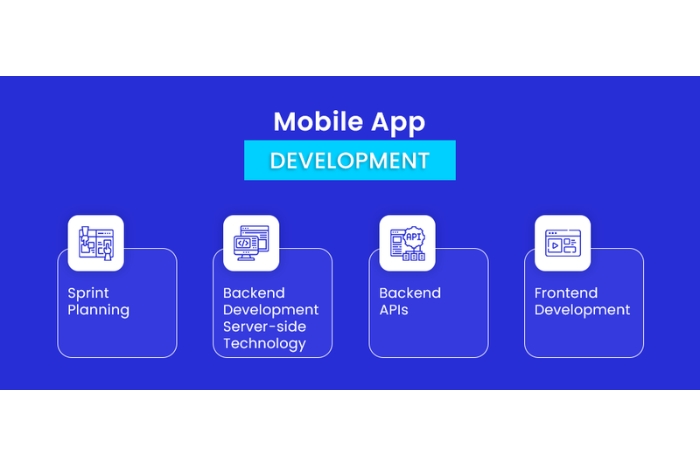
How to Hire a Mobile App Development Company in Canada (Complete Guide)
DevSecOps Pipeline in IoT Development
A DevSecOps pipeline integrates security into every stage of development. It starts from the first commit and continues through deployment and monitoring.
1. Code Commit Stage
Developers write code and push it to version control systems.
Security actions:
- Code linting
- Secret detection
- Dependency checks
This stage ensures that insecure code does not enter the pipeline.
2. Build Stage
The system compiles code and prepares firmware or applications.
Security actions:
- Static Application Security Testing (SAST)
- Dependency vulnerability scanning
This helps identify vulnerabilities in code and libraries.
3. Test Stage
Automated tests validate functionality and security.
Security actions:
- Dynamic Application Security Testing (DAST)
- API security testing
- Device simulation testing
This stage checks how the system behaves under different conditions.
4. Integration Stage
Different components connect and work together.
Security actions:
- Integration security testing
- Data flow validation
This ensures secure communication between systems.
5. Deployment Stage
Applications and firmware are deployed to devices and cloud platforms.
Security actions:
- Secure configuration checks
- Container security scanning
- Access control enforcement
6. Monitoring Stage
After deployment, systems require continuous monitoring.
Security actions:
- Threat detection
- Log analysis
- Incident response
This stage ensures long-term system security.
Key Components of a Secure IoT DevSecOps Pipeline
A secure IoT DevSecOps pipeline ensures that security is not an afterthought. It is integrated into every stage of device development, from initial design to deployment and ongoing maintenance.
To understand how this works in practice, let’s look at the key components that make up a robust and secure IoT DevSecOps pipeline.
1. Secure Code Practices
Developers follow secure coding standards to prevent vulnerabilities from entering the system. They also use code reviews and static analysis tools to identify and fix issues early in the development process.
2. Automated Security Testing
Security tests run automatically during development to detect vulnerabilities at each stage. This includes static and dynamic testing, which helps ensure that code changes do not introduce new risks.
3. Device Identity Management
Each device is assigned a unique identity for authentication and access control. This ensures that only authorized devices can connect to the network and exchange data securely.
4. Secure Communication
Data is protected using encryption during transmission between devices, gateways, and cloud systems. This prevents unauthorized access and ensures data integrity across the network.
5. Firmware Security
Firmware is signed and verified before updates are installed on devices. This ensures that only trusted and validated code runs on the hardware, reducing the risk of malicious updates.
6. Continuous Monitoring
Systems continuously track device behavior, network activity, and performance metrics. This helps detect anomalies, identify potential threats, and respond quickly to security incidents.
Role of an IoT Application Development Company
An IoT Application Development Services designs and manages secure IoT systems using DevSecOps principles.
Key responsibilities include:
- Architecture Design: They design secure system architecture for devices and the cloud.
- Pipeline Setup: They build automated DevSecOps pipelines for development.
- Security Integration: They integrate security tools at each stage.
- Compliance Management: They ensure systems meet industry standards.
- Maintenance and Updates: They manage updates and monitor system performance.
IoT App Development Services in DevSecOps
Modern IoT App Development Services include:
- Secure firmware development
- Cloud application development
- API integration
- Device management solutions
- Security testing and validation
These services focus on building secure and scalable IoT applications.
Real-World Example
Smart Manufacturing Use Case: A manufacturing company implemented IoT sensors to monitor equipment performance and detect failures in real time. While the setup improved visibility, it exposed several critical security gaps.
Challenges Faced: The devices did not have strong authentication, making them vulnerable to unauthorized access. Firmware updates were deployed without proper verification, increasing the risk of tampering. Additionally, data transmitted between devices and systems was not encrypted, leaving it exposed to interception.
Solution: An IoT Application Development Company implemented a DevSecOps pipeline.
- Added code security checks during development
- Enabled encrypted communication
- Introduced secure firmware signing
Results:
- Reduced security risks
- Improved system reliability
- Enabled safe remote updates
Benefits of DevSecOps in IoT
DevSecOps in IoT helps organizations build and manage connected devices with security integrated throughout the entire development lifecycle, reducing risks and improving system resilience.
To see its impact more clearly, let’s explore the key benefits of adopting DevSecOps in IoT environments.
- Early Risk Detection: Security issues are identified during development.
- Reduced Costs: Fixing issues early reduces overall cost.
- Faster Deployment: Automated pipelines speed up delivery.
- Improved Compliance: Systems meet security standards more easily.
- Continuous Security: Monitoring ensures ongoing protection.
Common Challenges in IoT DevSecOps
IoT DevSecOps comes with unique challenges due to the scale, diversity, and complexity of connected devices and systems.
To better understand these difficulties, let’s look at the most common challenges faced in IoT DevSecOps.
- Device Diversity: Different devices use different hardware and protocols.
- Resource Constraints: Devices have limited processing power.
- Complex Integration: Multiple systems must work together securely.
- Skill Gaps: Teams need expertise in development and security.
Best Practices for Secure IoT DevSecOps
A strong IoT DevSecOps approach depends on a few essential practices that ensure consistent security across the pipeline. Some of them are:
- Start security early by integrating it from the first code commit, so issues are caught before they grow.
- Automate testing to maintain continuous security validation without slowing development speed.
- Use strong authentication to give each device a secure and unique identity.
- Encrypt data end-to-end to protect it during both transmission and storage.
- Monitor continuously to track system behavior and quickly detect potential threats.
Future Trends in IoT DevSecOps
As IoT ecosystems grow more complex, security practices are evolving to become smarter, faster, and more adaptive. The following trends are shaping the future of IoT DevSecOps:
1. AI-Driven Security
Artificial intelligence is playing a larger role in identifying threats and unusual behavior in real time. Instead of relying only on predefined rules, AI can detect patterns and anomalies, helping teams respond to risks more quickly and accurately.
2. Edge-Centric Security
With more processing happening at the edge, security is shifting closer to the devices themselves. This reduces response time, limits data exposure, and ensures faster protection even when connectivity to central systems is limited.
3. Zero Trust Architecture
The traditional concept of trusting internal networks is being replaced. Every user, device, and request must be continuously verified before access is granted, reducing the risk of unauthorized entry and lateral movement within systems.
4. Automated Compliance Monitoring
Compliance is no longer a one-time checklist. Automated tools continuously monitor systems against regulatory standards, helping organizations maintain compliance, reduce manual effort, and quickly address any violations.
Conclusion
IoT systems continue to expand across industries. With this growth, security risks also increase. Traditional approaches cannot handle modern IoT challenges. An IoT Application Development Company uses DevSecOps pipelines to secure systems from the first commit. This approach ensures that security is built into every stage of development.











Leave a Reply